Imagine an employee joins your company today. Within the first hour, HR uploads their details into the system and instantly, without IT intervention, they’re granted access to email, Slack, Microsoft Teams, Salesforce, and the exact folder permissions they need. No more than that.
This is an ideal scenario. However, almost every organization today especially those operating across SaaS, hybrid cloud, and distributed teams is battling identity chaos. A growing number of users, countless applications, and access points that are no longer controlled. In 2024, 83% of organizations reported insider attacks.
This is where RBAC in Workforce IAM becomes critical for security, compliance, and productivity.
Workforce Identity and Access Management (IAM) is the strategic process of managing the digital identities of employees, contractors, and partners and controlling what they can access throughout their lifecycle (join, move, leave) within the organization.
It involves policies, strategies, and tools that ensure safe, compliant access to critical systems while protecting business data. With effective Workforce IAM, companies can mitigate risks of data breaches, insider threats, and mismanaged access.
This robust system empowers IT administrators to efficiently manage workforce identities and access privileges, ensuring secure, timely entry to applications and resources. Many modern IAM systems now leverage external identity providers for authentication, providing seamless and verified access control.
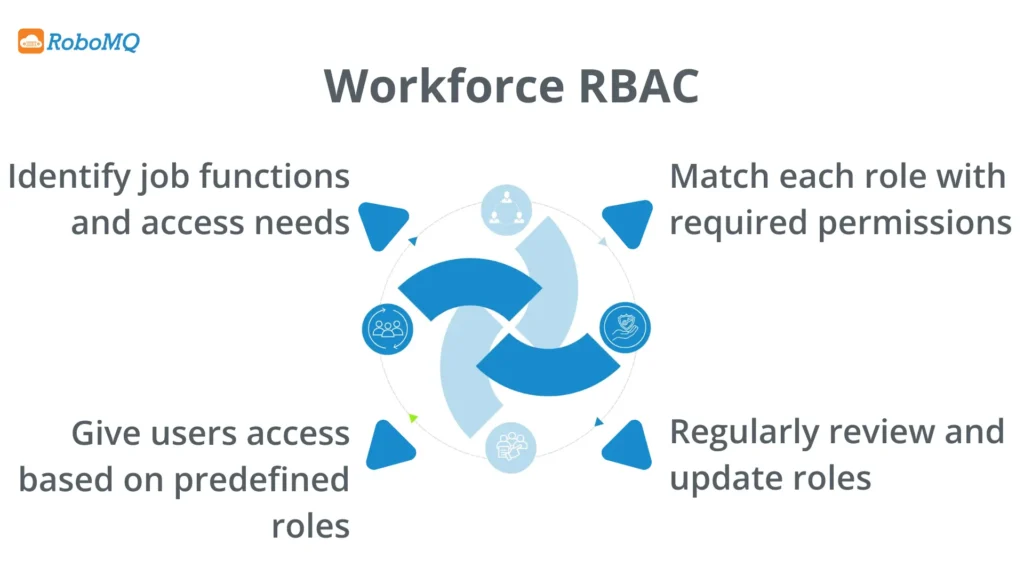
Among the most essential components of Workforce Identity and Access Management is Role-Based Access Control (RBAC), which defines and enforces access boundaries across the enterprise.
Role-Based Access Control (RBAC) is a framework that manages user access based on organizational roles. Rather than assigning permissions individually, RBAC groups permissions by job function so when a user is assigned to a specific role, they automatically inherit the corresponding access rights.
RBAC in Workforce IAM enforces the principle of Least Privilege Access, ensuring employees receive only the permissions they need nothing more. This helps organizations minimize security risks while simplifying user management and maintaining compliance.
Modern enterprises rely on dozens of SaaS and on-prem applications, making manual permission management impossible to scale. RBAC in Workforce IAM solves this by:
When paired with identity governance, RBAC provides both security and accountability for every workforce identity.
The National Institute of Standards and Technology (NIST), which developed the RBAC model, provides three basic rules for all RBAC systems.
These principles form the foundation of RBAC in Workforce IAM, ensuring structured, policy-driven access management across enterprise systems.
For the successful implementation of Role-Based Access Control (RBAC) in an Identity and Access Management (IAM) system, some prerequisites are required.
To guarantee a seamless and successful implementation, follow these crucial steps:
Identifying and defining roles within the organisation according to job functions and responsibilities is the first step in putting RBAC into practice. Every role should have a distinct set of permissions that correspond to the tasks that go along with it. This includes:
After defining roles, assign permissions using the Least Privilege Access principle to minimize exposure.
Assigning users to suitable roles according to their job functions and responsibilities comes after roles have been defined and permissions have been granted. This procedure involves:
Regularly review and maintain role definitions and permissions to align with organizational changes.
It is crucial to integrate RBAC with other security measures and put supporting policies in place to guarantee that RBAC is applied consistently throughout the company. This contains:
Continuous monitoring and auditing of user activities and access patterns are essential to detect anomalies and ensure compliance with security policies. This involves:
A hospital IT administrator creates an RBAC role for “Nurse.”
This demonstrates how RBAC in Workforce IAM ensures both operational efficiency and security integrity.
RBAC transforms Workforce Identity and Access Management by defining who gets access to what the moment they join, change roles, or leave. It ensures least-privilege access, eliminates manual IT dependency, streamlines audits, and scales effortlessly as organizations grow.
Enterprises adopting RBAC in Workforce IAM build a foundation of trust, security, and efficiency empowering a future-ready, compliant, and agile workforce.
HR systems act as the source of truth for employee roles, departments, and status. IAM platforms automatically use this HR data to provision or revoke access based on predefined RBAC roles, ensuring access is always aligned with the employee’s current job function.
RBAC enforces least privilege access, ensuring employees only receive access strictly relevant to their role nothing more. This eliminates excessive permissions, reduces attack surface, and prevents intentional or accidental misuse of high-risk access.
Together, RBAC and Workforce IAM automate access control, eliminate manual IT dependency, accelerate onboarding, and ensure real-time access governance — transforming identity security from reactive to proactive, while boosting workforce productivity and compliance.
Hire2Retire automates role-based access control (RBAC) by syncing roles directly from your HR system. As employees join, move, or exit, their access privileges update instantly no manual intervention or IT tickets required.
You can watch the Hire2Retire video guide to explore how it automates employee lifecycle management and access governance from hire to retire.