In many organizations, one in four audit findings trace back to access that stayed active longer than it should have. Not because of attackers, but because of broken workflow timing.
Imagine a scenario where a senior employee resigns on Friday. HR updates the system the same day. But IT plans to remove access on Monday because that is when the ticket is scheduled. Over the weekend, the employee’s VPN and cloud access remain active. Nothing happens. But it could have.
This is how risk enters an organization. Not through dramatic attacks, but through small process gaps. A weak hire to retire process flow creates silent vulnerabilities. Access remains longer than it should. Permissions are not updated after role changes. Audit logs are incomplete. Over time, these small gaps grow into compliance failures and security incidents.
Companies invest heavily in cybersecurity tools. Yet if the hire to retire workflow is not structured and connected, those tools cannot fully protect the organization. Understanding how the hire to retire end-to-end process affects compliance and security is critical for modern enterprises.
Onboarding and offboarding are often treated as HR activities. They are security events. The hire to retire process flow determines how employee lifecycle changes move across systems. When HR updates a record, that change should automatically trigger access provisioning, modification, or revocation in IT and security systems.
If this connection is manual or fragmented, risk increases. In many organizations, the hire to retire workflow depends on emails, spreadsheets, or service tickets. HR informs IT. IT informs security. Each handoff introduces delay and room for error.
When this happens:
A structured hire to retire process ensures that identity changes are handled consistently and tracked properly. Identity is the front door to every system. If that door is not controlled properly, compliance and security both suffer.
A weak hire to retire process typically fails in predictable areas.
According to the 2023 IBM Cost of a Data Breach Report, the global average cost of a data breach reached $4.45 million. Compromised or misused credentials are among the most common causes. Weak lifecycle management directly contributes to this risk. A broken hire to retire workflow makes it difficult to control who has access and when that access should end.
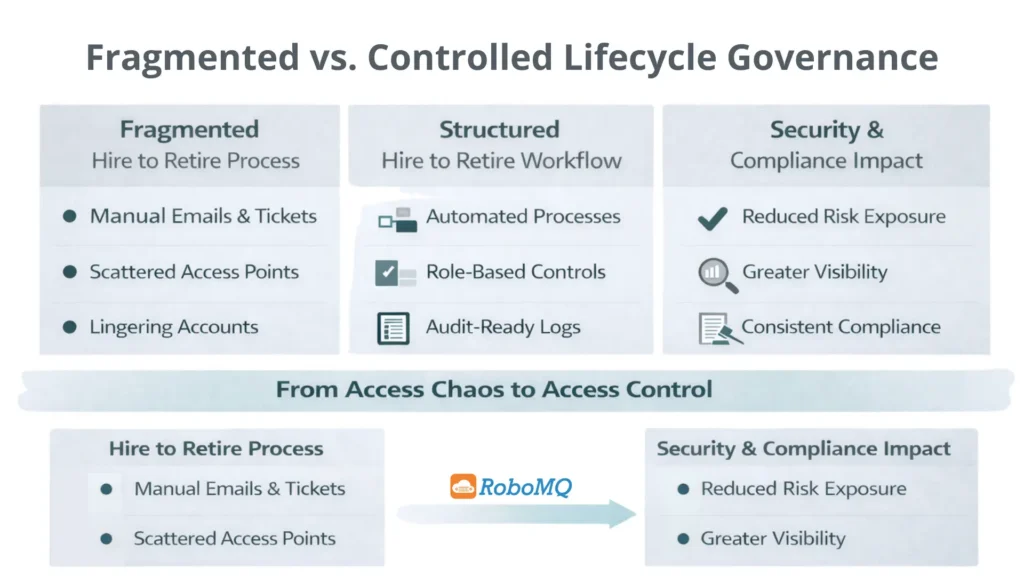
To make this clearer, consider the difference between a fragmented hire to retire end-to-end process and a structured one.
| Lifecycle Stage | Fragmented Hire to Retire Process Flow | Structured Hire to Retire Workflow | Security & Compliance Impact |
|---|---|---|---|
| Onboarding Trigger | HR informs IT manually | HR system triggers automated workflow | Reduces delay and manual errors |
| Account Creation | IT creates accounts one system at a time | Automated provisioning across connected systems | Faster and more accurate setup |
| Role-Based Access | Access assigned individually | Access mapped to defined job roles | Prevents excess permissions |
| Role Changes | Old access often remains | Access updated automatically | Reduces unnecessary access |
| Temporary Access | Managed informally | Time-based access with automatic expiry | Limits long-term exposure |
| Offboarding | Manual request to revoke access | Automatic deprovisioning triggered by HR event | Prevents orphaned accounts |
| Audit Logs | Stored in tickets and emails | Centralized and time-stamped records | Stronger audit readiness |
| Policy Enforcement | Depends on individuals | Enforced by system rules | Consistent compliance control |
The difference is not only operational efficiency. It directly affects security posture and audit readiness.
Consider a contractor whose project ends on the 30th of the month. HR makes a correct record of the contract end date. However, the hire to retire process flow depends on a manual ticket for access removal. The ticket gets delayed. The contractor’s access is left active for ten days after the end of the contract.
The contractor has access to sensitive project files during those ten days. Even if there is no misuse, the organization is at risk. If an audit takes place, there is no clear record showing timely deprovisioning.
This is how small process gaps turn into compliance findings. The issue is not a lack of security tools. It is a weak hire to retire workflow that does not automatically connect HR events with access controls.
Access control is a major aspect of regulatory compliance. Standards such as ISO 27001, SOC 2, HIPAA, and GDPR require:
It is very challenging to accomplish these requirements when the hire to retire process is poorly managed.
Manual processes are hardly ever equipped to produce complete logs of activities. When auditors ask for proof of the timings of an access removal, the organization has a hard time producing trustworthy evidence.
Without automation, the existence of conflicting permissions may not be detected. This raises the level of fraud and policy violation risk.
Policies that depend on manual execution are applied unevenly. A structured hire to retire process ensures consistency.
Compliance depends on repeatable and traceable processes. A mature hire to retire workflow delivers both.
Most organizations improve the hire to retire process flow to avoid breaches and audit penalties. That is important, but it is not the full picture. A strong hire to retire workflow also improves speed and trust. New employees become productive on day one because access is ready. Role transitions happen smoothly. Leadership gains real-time visibility into who has access across systems.
When the process is automated and connected, the organization moves faster without losing control. Security stops being a bottleneck. It becomes an enabler. Companies that manage identity lifecycle well do not just reduce risk. They build operational confidence. And confidence supports growth.
Solutions such as Hire2Retire help organizations connect HR systems with IT and security platforms to automate lifecycle events. By orchestrating the process flow end to end, such platforms reduce manual intervention, improve audit visibility, and ensure timely access changes across systems.
Security tools cannot compensate for a broken process. If the process flow is weak, access remains uncontrolled. If access is uncontrolled, compliance becomes difficult. If compliance is weak, risk increases. Identity lifecycle management is not only an HR or IT function. It is a business risk control. Boards discuss cyber risk. Regulators review access governance. Auditors request proof. All these concerns connect back to how well the hire to retire workflow is managed.
A structured hire to retire end-to-end process ensures that the right people have the right access at the right time, and that access is removed when it is no longer needed. In today’s digital environment, controlling identity means controlling risk. Strengthening the hire to retire process flow is one of the most practical and impactful steps an organization can take to protect data, maintain compliance, and support growth.
A hire to retire process flow defines how employee lifecycle events such as hiring, role changes, and termination trigger access-related actions across HR, IT, and security systems.
Onboarding focuses only on new hires. A hire to retire workflow covers the full employee lifecycle, including internal movement and offboarding.
It includes hiring, access provisioning, role updates, periodic access reviews, and deprovisioning when employment ends.
Because delayed or incomplete access changes can lead to privilege accumulation, orphaned accounts, and lack of audit visibility.
Organizations can improve their hire to retire workflow by connecting HR systems with identity platforms, automating access provisioning and removal, and applying role-based controls with centralized audit tracking. This reduces manual effort and closes common security gaps.
Hire2Retire brings all of this together by ensuring access is granted and removed on time, while maintaining complete visibility and compliance across the employee lifecycle.