Nearly 43% of companies fail to fully revoke access for ex-employees, allowing them to retain entry to sensitive systems like code repositories.
Paul, a senior data analyst at Noventrix Corp, wraps up his final day on the job. HR sends him a polite goodbye email, and IT disables his VPN at 6 p.m. Everything seems in order.
But an hour later, Paul can still access his corporate email, internal Slack, and even an old database that stores sensitive IP. Days later, the system flags unusual activity on that very database. By then, it’s too late, data may have been leaked, contracts exposed, and regulators are knocking on Noventrix’s door.
This scenario is not fiction; it’s what happens when organizations lack strong Identity Lifecycle automation. In today’s interconnected workplaces, employee lifecycle management and identity governance (IGA) are essential pillars of enterprise security.
When identity control fails, attackers find open doors. Weak or lingering accounts allow impersonation, privilege escalation, and stealthy data access that can last for months undetected.
According to reports, the average data breach lifecycle, detection plus containment, spans hundreds of days. Nearly 74% of breaches involve compromised credentials, proving that identity risk is the new frontline of cybersecurity.
And the impact is beyond financial loss, a single identity breach can destroy years of customer trust and invite severe regulatory scrutiny.
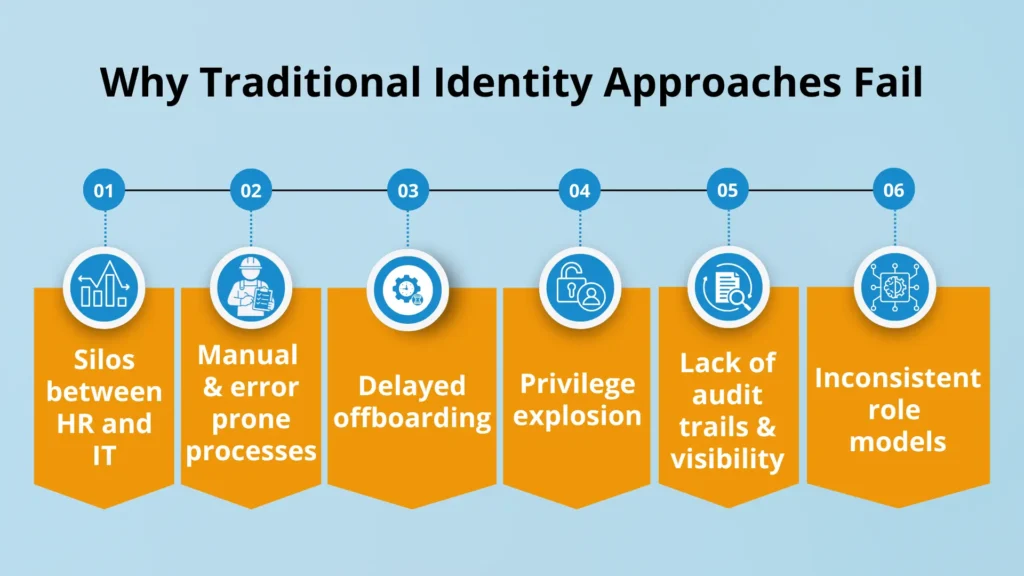
Let’s dissect the main issues to better understand:
The consequences are serious: data exfiltration, fines from regulators (GDPR, HIPAA, SOX), exposure to lawsuits, the loss of IP, and damage to trust.
Identity Lifecycle Management is the automated, controlled and audited process of managing digital accounts, from creation (member acquisition), by a user changing their role (role movement), to deactivation (deactivation). It is integrated with Employee Lifecycle Management (the HR-started events of join, move, leave).
Core elements of a good ILM framework:
1: Onboarding / Provisioning: Create accounts immediately, add default roles, group memberships, and licenses.
2: Mid-life changes (Move / Update): Change roles, access, new apps, or old ones.
3: Offboarding / Deprovisioning: Prompt revocation of access immediately across all systems.
4: Privileged identity controls: Additional security features for admin-level accounts.
5: Audit and reporting & compliance: Visibility throughout the identity journey.
ILM closes the windows of exposure very narrowly by automatically enforcing policies at every step.
Hire2Retire is a Lightweight IGA (Identity, Governance and Administration) product that manages workforce lifecycle from HR systems to Active Directory, Entra ID, Okta and Google Directory provisioning identity, privilege, 3rd party system access, and assets and resources to automate onboarding, offboarding and role transition to provide superior first day at work, reduce operational cost, mitigate security & compliance risk and help improve security posture.
What Hire2Retire does:
Let’s come back from Noventrix Corp and Paul’s departure with ILM in place.

At 6:01 pm, Paul no longer has access to anything sensitive. Because his credentials no longer function, an attacker can’t abuse them. The enterprise escaped exposure, and the security team ended up sleeping better that night.
But this is where identity lifecycle management takes us from theory to real-world defence. Identity cannot remain a cosmetic IT function for modern enterprises. The identity perimeter is the new security frontier – the new security moment, and every hire, role change, and exit is a security moment.
Solutions such as Hire2Retire allow organizations to align HR and IT in real-time, automate provisioning and deprovisioning, enforce least privilege with full auditability, reduce human error and orphan accounts, and get measurable ROI through lower breach risks and operational efficiency.
If you want to grow your identity perimeter, lower risk and close the HR-IT divide, Hire2Retire is worth researching.
They fail due to silos between HR and IT, relying on manual, error-prone processes, leading to delayed offboarding, and suffering from a lack of audit trails and visibility.
The main risk is compromised credentials and lingering accounts (especially from ex-employees), which attackers use for impersonation, privilege escalation, and stealthy data access.
It’s the problem where users accumulate access rights over time as they change roles, retaining old permissions they no longer need, which increases the security exposure window.
It shrinks the security exposure window by automating access provisioning and near real-time deprovisioning, and it enforces the Principle of Least Privilege.
Hire2Retire is a Lightweight IGA product that automates the entire workforce lifecycle by syncing events from HR systems (Hire/Move/Leave) to identity platforms for immediate access control.

Sujata Swarnim is a Marketing Enthuasiast with a majors in Marketing , working at RoboMQ. She thrives on connecting the dots, between people, ideas & opportunities - turning creative insights into meaningful impact & power brand stories.

Sujata Swarnim is a Marketing Enthuasiast with a majors in Marketing , working at RoboMQ. She thrives on connecting the dots, between people, ideas & opportunities - turning creative insights into meaningful impact & power brand stories.