Posted onDecember 12, 2025
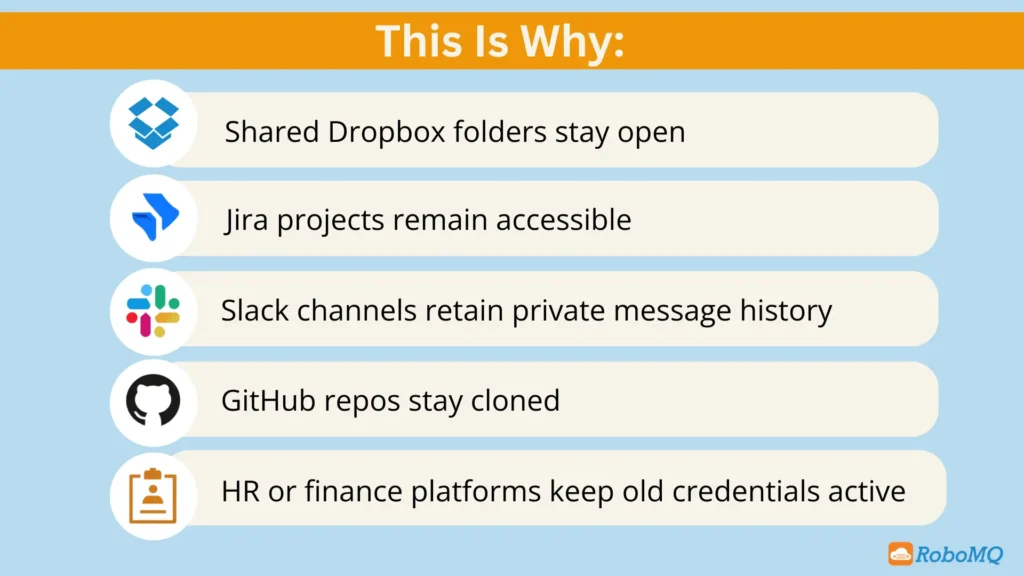
How To Why Most Offboarding Processes Fail After Day One Use Cases Sujata Swarnim December 12, 2025 Offboarding should be simple: someone leaves, and their access goes with them. But in most organizations, that’s not what actually happens.On day one, visible accounts...

Why IAM, IGA, and PAM Fail and How to Fix Them
Posted onDecember 4, 2025
How To Why IAM, IGA, and PAM Fail and How to Fix Them Use Cases Sujata Swarnim December 4, 2025 Identity security is getting harder, not easier. Enterprise apps have multiplied, remote access is normal, and privileged accounts are everywhere. Yet most companies still...

Hybrid Workforces and the New Identity Security Risks
Posted onDecember 3, 2025
How To Hybrid Workforces and the New Identity Security Risks Use Cases Sujata Swarnim December 3, 2025 Companies spent three years building systems for remote work. Now they’re shifting employees back to offices – part-time, full-time, or somewhere in-between....

Least Privilege and the Risk You Don’t See Coming
Posted onDecember 3, 2025
How To Least Privilege and the Risk You Don’t See Coming Use Cases Sujata Swarnim December 3, 2025 “Least privilege” seems like a no-brainer: give people just enough access to do their job – and nothing more. In theory, it reduces risk, limits damage from...

HR Data Sync for Enterprises: What’s Broken and Why?
Posted onNovember 27, 2025
How To HR Data Sync for Enterprises: What’s Broken and Why? Use Cases Sujata Swarnim November 27, 2025 Every company wants fast onboarding, clean audits, and smooth identity access, yet most of them are still running on HR processes that drifts, breaks, or simply...