What happens when employees keep access to systems, they no longer need or gain access they should never have had in the first place? Scary thought, right? Well, in growing enterprises, controlling user permissions across dozens of applications is difficult. This is where identity governance and administration tools play a critical role.
They help organizations bring structure, visibility, and control to user access. IGA tools ensure that the right people have the right permissions at the right time while reducing security risks and supporting compliance.
Today, we will explore the key features and capabilities of identity governance and administration tools. We’ll also know how they help organizations manage access more securely and efficiently.
Identity governance and administration tools are systems that keep track of users’ identities, control who has access to what, and make sure that security policies are followed throughout a company. They take care of the whole employee lifecycle, from onboarding to offboarding.
The current IT landscape comprises multiple systems, both on-premises and in the cloud, causing challenges for organizations in managing identity governance. One of the biggest challenges is trying to manage access to all these applications manually. Identity governance solutions help organizations to control, automate, and audit user access across systems. They help companies address their identity-related challenges, including:
Platforms such as Hire2Retire enable organizations to automate their identity lifecycle processes and provide consistent governance over their associated HR and IT systems. It’s a lightweight IGA tool that automates the entire employee lifecycle, from onboarding to role changes to offboarding.
Now that we know what identity governance and administration tools are and why businesses need them, let’s discover some of the core features of an IGA solution.
identity governance and administration tools manage the complete employee lifecycle within the company. This includes employee onboarding, role changes, and offboarding. As employees come on board, move to a new role, or leave the company, IGA solutions automatically update their access permissions. This ensures that employees always have the correct access, eliminating the risk of employees having access to accounts that should no longer be active.
Employees can request access to applications and resources through a user-friendly self-service portal. The system automatically routes the request to an appropriate manager or system owner based on corporate policy. Once approved, access is granted without any manual IT work.
identity governance and administration tools automatically provision (create) and deprovision (remove) user accounts in your business systems, streamlining the entire employee journey from joining and moving to leaving. When a new employee joins the company, the IGA system will provide that employee with the required access to systems. When that same employee leaves the company, all access will be removed immediately. This will help to reduce overall risk and significantly reduce the effort for your IT teams.
Role-based access control (RBAC) is when roles are assigned to users so that they can access only the information required to do their job properly. For example, if a user is in the finance department, they would be given login access to the company’s financial data. If a user is in the HR department, they would be given access to HR-specific information.
Entitlement Management defines what users can do within application systems. Some users will only be able to see the data, while others will be able to edit the data, approve the data, or even manage the data. This helps keep control over the use and access to sensitive information.
Identity Governance and Administration (IGA) solutions allow organizations to systematically review who has access to sensitive systems and applications. Through these reviews, managers can determine if the user still requires access and removes access, if not required. Maintaining compliance with both internal and external policies is just one of the ways to ensure that you comply with regulatory requirements.
SoD is a control that eliminate the risk of a single employee being able to both approve and conduct a financial transaction. SoD policies provide accountability while safeguarding sensitive business activities. IGA solutions enforce segregation of duties by checking access requests, roles, and entitlements against defined SoD policies across the identity lifecycle.
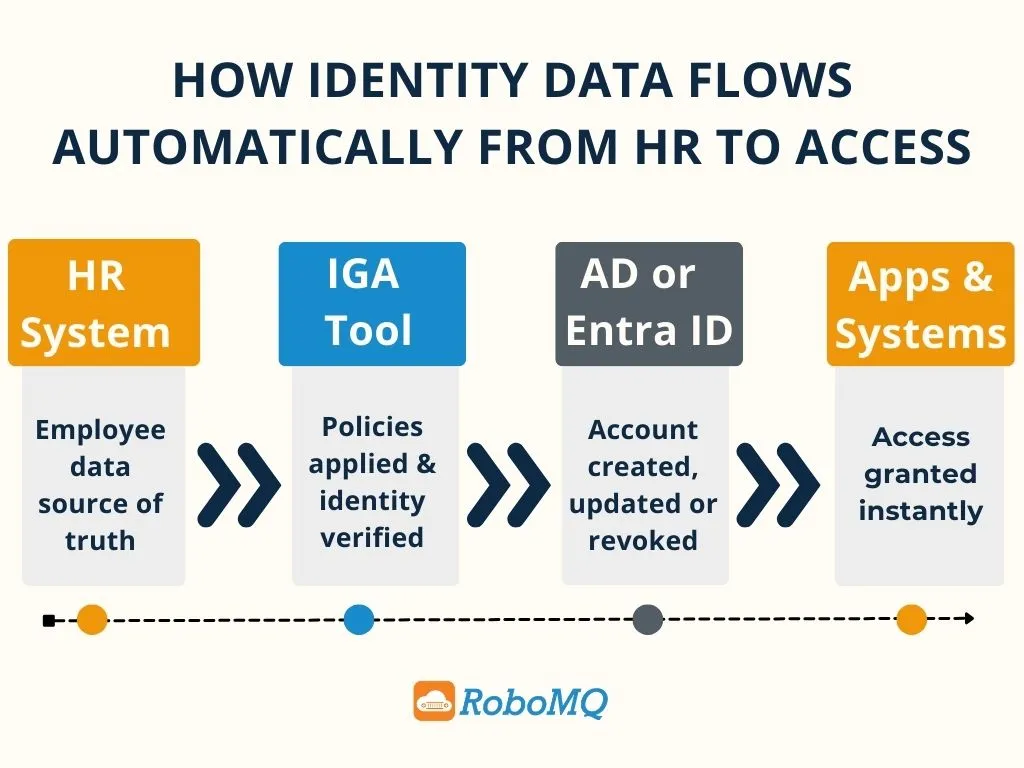
By using identity governance and administration tools, companies can easily integrate their HR platforms, directories, enterprise applications, and many more by connecting these systems with IGA. This means that as company employees access information through any of these systems, their access rights and other data will automatically be updated on both the IGA system and the source systems without having to manually update each time an employee accesses one of these systems.
Employees can use a single identity to log into all applications they need. This means that after logging into the system once, they can access all other applications without having to create or manage a separate identity/password for each application. This reduces their fatigue due to managing multiple passwords and significantly simplifies their ability to access applications.
IGA systems provide organizations with detailed reports of user access and activity. This allows companies to monitor who accesses which systems and generate reports for compliance and auditing purposes quickly. Also, these reports can provide the organization with details on potential security breaches.
Today’s identity governance and administration tools utilize artificial intelligence to recognize unusual access patterns and/or potential security risks. In addition, AI offers recommendations for proper access levels and highlights access that may require urgent or increased oversight.
When companies implement identity governance and administration tools, they gain major enhancements to security, compliance, and long-term operational performance. Some of the major benefits include:
By using IGA, employees can only see and have access to the data, systems, or resources necessary to perform their job functions. Organizations will increase their chances of preventing internal threats by enforcing the principle of least privilege and removing user access to old permissions automatically. Thus, reducing the risk of unauthorized access to sensitive company information.
Having an IGA solution will assist companies in fulfilling regulatory compliance requirements. Examples of ways to ensure regulatory compliance would include maintaining a record of user access logs and automated audit trails. Ongoing reviews of user access and periodic certification of user access ensure that employee permissions are still in compliance with security policies and regulatory compliance.
Automated provisioning enables an organization to provide system access to new employees on their first day of employment. This enables them to become productive as soon as they start working, which increases employee satisfaction.
While implementing identity governance and administration tools automates many of the routine tasks that are part of Identity Management (e.g., account creation, permission changes, and access removal), the number of manual requests for IT assistance will decline significantly, allowing IT teams to focus on providing value-added support to the business.
IGA systems give organizations centralized visibility into their user identities, existing user permissions at the system level, and user management capabilities. As per research, 64.4% businesses report that the complexity of handling user permissions across multiple systems is one of the top issues they want to solve with identity governance and administration tools. Security can now monitor users’ access to systems, determine any risks associated with user access, and provide an enterprise-wide enhanced level of access control.
Identity lifecycle management tools act as a central place to view all user accounts and accesses. This is a great for security team as they can track users, control their system access, and implement enterprise-level access control policies. However, to get the best benefits out from an IGA tool, you must choose it wisely. Not every IGA solution fits every company. So, here a few questions you must ask before picking any IGA tool.

With the growing digital systems of organizations, the complexity of handling users and their access increases. Identity governance and administration tools support organizations in maintaining secure access to systems, easing compliance with various regulatory requirements, and automating identity management processes.
Solutions like Hire2Retire by RoboMQ help organizations take this further by automating the entire workforce identity lifecycle. From onboarding and role changes to offboarding, this platform keeps HR and IT systems synchronized. Would you like to learn more? Contact us to set up a free demo and learn how Hire2Retire can maximize your organization’s identity governance effectiveness.
The key components of the Identity Governance and Administration (IGA) system are access provisioning and deprovisioning, access certification and review, role-based access control, segregation of duties (SoD), and transparent reporting.
IGA helps in improving the overall security of the organization by ensuring that only the required level of access is provided to the user. This helps in restricting the user from accessing the organization’s resources without authorization and also ensures that no individual is provided with more than the required level of access to perform his or her job functions.
The best practice for the identity governance and administration system is least privilege access, role-based access control, user onboarding and offboarding, access review and certification, and audit trails.
Some of the trends that are shaping the future of IGA are AI-based identity analytics, automation of access management, integration of IGA with cloud and SaaS applications, and a closer fit with zero trust security models. These are the trends that are shaping the future of IGA to help organizations manage identities in a smarter way.
Choosing the right IGA tool depends on factors such as your organization’s size, existing IT ecosystem, integration capabilities, scalability, and compliance requirements. It’s important to evaluate how well the solution can automate identity lifecycle processes, integrate with HR and IT systems, and support future growth while maintaining security and ease of use.